What is the SMB protocol?
What is the SMB protocol?
SMB stands for “Server Message Block.” It’s a file sharing protocol that was invented by IBM and has been around since the mid-eighties. The SMB protocol was designed to allow computers to read and write files to a remote host over a local area network (LAN).
Why we use SMB protocol?
The SMB protocol enables applications and their users to access files on remote servers, as well as connect to other resources, including printers, mailslots and named pipes. SMB provides client applications with a secure and controlled method for opening, reading, moving, creating and updating files on remote servers.
What is SMB1 and SMB2 protocol?
In case you’re not familiar, SMB stands for Server Message Block, and it’s a protocol for sharing files, and it has two versions, the SMB1, and the SMB2, the latter is the more secure one.
Does SMB use TCP or UDP?
Summary. Windows supports file and printer-sharing traffic by using the SMB protocol directly hosted on TCP. SMB 1.0 and older CIFS traffic supported the NetBIOS over TCP (NBT) protocol supported the UDP transport, but starting in Windows Vista and Windows Server 2008 with SMB 2.0. 2, requires TCP/IP over port 445.
Is SMB protocol Secure?
An information worker’s sensitive data is moved by using the SMB protocol. SMB Encryption offers an end-to-end privacy and integrity assurance between the file server and the client, regardless of the networks traversed, such as wide area network (WAN) connections that are maintained by non-Microsoft providers.
Is SMB still used?
SMB2 has now become SMB3. This is more of a marketing move since SMB3 still uses the MS-SMB2 protocol spec. There were just enough changes between SMB 2.1 and SMB 3.0 to justify a new major version. On an interesting historical note, SMB3 was originally SMB 2.2 until the marketing team got involved.
Where is SMB protocol used?
The Server Message Block (SMB) protocol is a network file sharing protocol that allows applications on a computer to read and write to files and to request services from server programs in a computer network. The SMB protocol can be used on top of its TCP/IP protocol or other network protocols.
How secure is SMB?
What type of protocol is SMB Tryhackme?
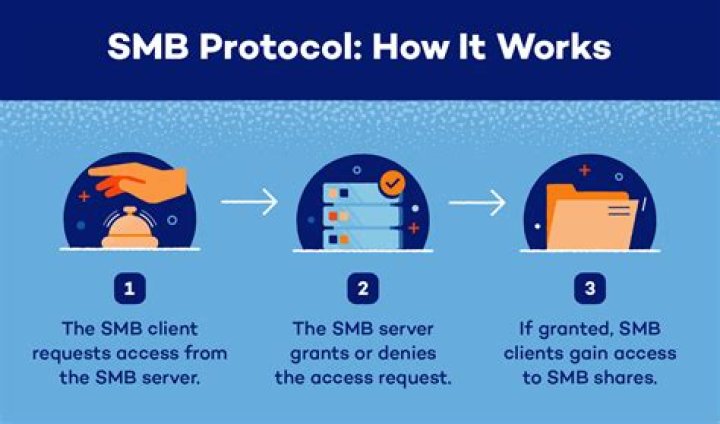
The SMB protocol is known as a response-request protocol, meaning that it transmits multiple messages between the client and server to establish a connection. Clients connect to servers using TCP/IP (actually NetBIOS over TCP/IP as specified in RFC1001 and RFC1002), NetBEUI or IPX/SPX.
What ports are used for SMB?
As such, SMB requires network ports on a computer or server to enable communication to other systems. SMB uses either IP port 139 or 445. Port 139: SMB originally ran on top of NetBIOS using port 139.
Why is SMB so vulnerable?
A vulnerability has been discovered in Microsoft Windows SMB Server that could allow for remote code execution. This vulnerability is due to an error in handling maliciously crafted compressed data packets within version 3.1. 1 of Server Message Blocks.
Does SMB use TLS?
Server Message Block (SMB) is a remote file-sharing protocol used by Microsoft Windows clients and servers. You can use LDAP over SSL/TLS to secure communication between the Storage Virtual Machine (SVM) LDAP client and the LDAP server.
The SMB is a network protocol which is also known as the Server Message Block protocol. It is used to communicate between a client and a server. It can be used to share the files, printers and some other network resources. It was created by IBM in the 1980s.
How to exploit SMB with NTLM hash capture?
Another method to exploit SMB is NTLM hash capture by capturing response password hashes of SMB target machine. This module provides an SMB service that can be used to capture the challenge-response password hashes of SMB client systems.
What versions of SMB are used in Windows Server?
SMB 2.1 / SMB2.1: This version used in Windows 7 and Windows Server 2008 R2. SMB 3.0 / SMB3: This version used in Windows 8 and Windows Server 2012. SMB 3.02 / SMB3: This version used in Windows 8.1 and Windows Server 2012 R2. SMB 3.1: This version used in Windows Server 2016 and Windows 10.
Is the target machine vulnerable to MS17-010 due to SMBv1?
As result, it has shown the target machine is highly vulnerable to Ms17-010 (eternal blue) due to SMBv1. As we know it is vulnerable to MS17-010 and we can use Metasploit to exploit this machine.